Safely storing cryptocurrency is one of the most important aspects of being a digital asset investor. Unlike traditional bank accounts, crypto transactions are irreversible and the responsibility for protecting your private keys ultimately rests with you—unless you outsource it to a custodian. The method you choose can significantly affect your security, accessibility, and even your estate planning.
Below, we’ll explore popular storage options, how they work, and the pros and cons of each.
1. Hardware Wallets: Ledger & Trezor
What They Are
Hardware wallets are physical devices that store your private keys offline, often in a secure chip. The two most popular brands are Ledger (Ledger Nano S Plus, Ledger Nano X) and Trezor (Trezor One, Trezor Model T).
How They Work
When you set up a hardware wallet, it generates your private keys internally and never exposes them to your computer or the internet. Transactions are signed within the device and only the signed transaction is sent to the blockchain via your connected app.
Advantages
- Security: Keys are never online, making them immune to most malware and phishing attacks.
- Control: You maintain full ownership of your funds without a third party.
- Compatibility: Support for multiple cryptocurrencies and DeFi integrations.
Risks
- Physical Loss or Damage: If you lose the device and your recovery seed, funds are gone.
- Phishing & Supply Chain Attacks: Fake apps, counterfeit devices, or compromised packaging can be a threat.
- Learning Curve: Requires some setup knowledge.
Best Practices
- Always buy from the official store.
- Keep your 12/24-word recovery seed offline and never store it digitally.
- Update firmware only from the manufacturer’s official site.
2. Paper Wallets
What They Are
A paper wallet is simply a physical printout of your public and private keys (or a QR code that encodes them).
How They Work
Keys are generated offline—often using an air-gapped computer and open-source wallet generator—then printed. The idea is to store the printout in a secure location.
Advantages
- Cold Storage: Fully offline, immune to online hacks.
- Low Cost: No special hardware required.
- No Third-Party Dependence: You generate and store your keys yourself.
Risks
- Physical Fragility: Paper can burn, fade, get wet, or tear.
- User Error: Generating keys securely is non-trivial; printing from an internet-connected device defeats the purpose.
- Single Point of Failure: If it’s lost or destroyed, funds are irretrievable.
Best Practices
- Use acid-free archival paper and high-quality ink.
- Store in a safe, waterproof container.
- Consider laminating, but avoid static build-up near electronics.
3. Multisignature Wallets (Multisig)
What They Are
A multisig wallet requires multiple private keys to authorize a transaction—e.g., 2 of 3, 3 of 5 signatures.
How They Work
Funds are held in a smart contract or special address that won’t release them unless the required number of private keys sign the transaction. The keys can be held by different people or devices.
Advantages
- Enhanced Security: A thief would need to compromise multiple keys in different locations.
- Shared Control: Ideal for business treasuries, joint accounts, or inheritance planning.
- Customizable Thresholds: Flexible signing rules.
Risks
- Complex Setup: More technical than single-key wallets.
- Coordination: All required signers must cooperate for transactions.
- Software Risk: Bugs in multisig smart contracts or wallet code.
Best Practices
- Distribute keys across secure, unrelated locations/devices.
- Use reputable wallet providers (e.g., Casa, Unchained, Electrum multisig).
- Document the signing process clearly for all participants.
4. Custodial Storage
What It Is
A third party—such as an exchange or specialized custodian—holds your private keys for you.
How It Works
You have an account with the custodian. They manage the keys and typically offer insurance, compliance, and support services.
Advantages
- Ease of Use: No need to manage keys yourself.
- Recovery Options: Lost password recovery is possible.
- Institutional-Grade Security: Cold storage, multi-sig, geographic key distribution.
Risks
- Counterparty Risk: If the custodian is hacked, insolvent, or dishonest, you could lose funds.
- Regulatory Seizure: Funds can be frozen or confiscated.
- No Sovereignty: “Not your keys, not your coins.”
Best Practices
- Use regulated, insured custodians.
- Limit custodial storage to assets you actively trade.
- Diversify—don’t keep all your crypto in one custodian.
5. ETFs as Indirect Storage
What They Are
Cryptocurrency ETFs (Exchange-Traded Funds) let you gain exposure to crypto prices without holding the coins yourself.
How They Work
An ETF issuer holds crypto (spot) or crypto futures. You own shares in the ETF, not the underlying crypto. This removes all key management responsibilities.
Advantages
- No Wallet Management: The issuer handles custody.
- Regulated Product: Traded on stock exchanges.
- Ease of Integration: Fits into traditional portfolios.
Risks
- No Direct Ownership: You can’t withdraw the crypto to use on-chain.
- Management Fees: Expense ratios reduce returns.
- Counterparty & Regulatory Risk: ETF custodian or policy changes could impact value.
Best Practices
- Use ETFs for price exposure, not long-term sovereign holding.
- Compare expense ratios and tracking accuracy.
- Understand that this is not “storing” crypto in the traditional sense.
6. Crypto Steel & Metal Backups
What It Is
A physical backup medium made of stainless steel or titanium that stores your recovery seed words.
How It Works
You engrave, stamp, or assemble your recovery phrase into a metal plate. This makes it resistant to fire, water, corrosion, and other physical threats.
Advantages
- Durability: Survives extreme conditions.
- Longevity: Metal outlasts paper and ink.
- Offline Security: Immune to hacks.
Risks
- Physical Theft: If someone finds it and recognizes it, they can steal your funds.
- Cost: More expensive than paper.
- Setup Errors: Mistakes during stamping or assembly can ruin legibility.
Best Practices
- Store in a discreet, secure location (safe, deposit box).
- Avoid engraving wallet names or obvious crypto symbols.
- Use multiple backups in geographically separate locations.
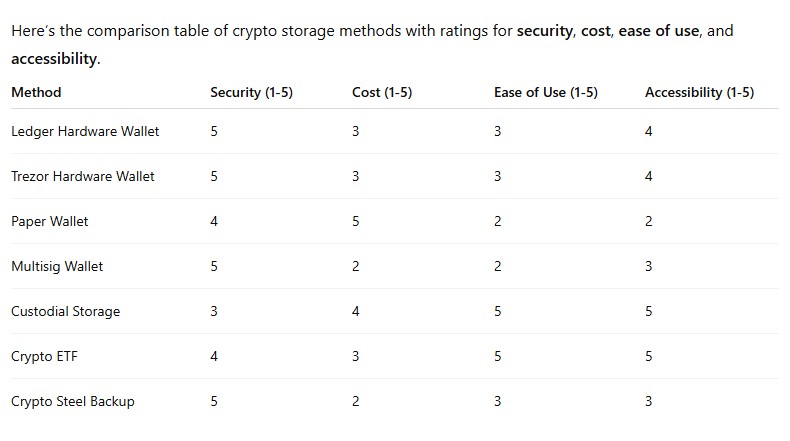
7. Choosing the Right Storage Mix
The ideal storage solution depends on your priorities:
- Security Above All: Hardware wallet + crypto steel backup + multisig.
- Ease of Use: Custodial storage or ETF.
- Long-Term Cold Storage: Paper wallet or hardware wallet in a safe, with seed on crypto steel.
- Institutional/Business: Multisig with distributed key holders and professional custody.
Many experienced holders use a layered approach:
- A hot wallet (software or exchange account) for small, daily-use funds.
- A cold wallet (hardware or paper) for savings.
- Redundant backups (crypto steel in two locations).
- Multisig for high-value vaults.
8. Security Principles for All Methods
No matter the storage method, these rules apply:
- Control Your Keys: If someone else holds them, you don’t own your crypto.
- Back Up Securely: Store multiple copies in safe, geographically separate places.
- Use Strong Physical Security: Safes, security deposit boxes, alarm systems.
- Stay Updated: Firmware updates, best practices, threat awareness.
- Plan for Inheritance: Document recovery steps for heirs without compromising security.
New Hardware Wallets To Consider
Keystone — Open-Source, Air-Gapped Security
The Keystone line of hardware wallets (including the Keystone 3 Pro) is designed for high-security, offline storage:
- Air-gapped cold storage: Keystone devices never connect to the Internet directly, keeping private keys completely offline.
- Open source: Firmware transparency helps the community audit the code — a strong plus for trust and verification.
- Touchscreen & QR signing: Intuitive touchscreens and QR-based interactions improve usability without sacrificing security.
Keystone also offers metal backup tools (e.g., steel seed-phrase plates) to protect your recovery phrase against fire or water damage, which is a best practice for long-term self-custody.
Tandem Wallet — Simple & Practical Cold Storage
Tandem (sometimes seen spelled Tangem) wallets take a smart-card approach to storage:
- NFC contactless design: Like a bank card, Tandem hardware stores private keys securely and signs transactions via close-range NFC.
- Battery-free & mobile-friendly: No cables or batteries — you manage assets easily on iOS/Android apps without exposing keys to online threats.
- Multiple asset support: Tandem devices can hold thousands of tokens across dozens of blockchains.
This approach appeals to users who want physical wallets that are convenient yet secure without the complexity of USB or Bluetooth connections.
Conclusion
From Ledger and Trezor hardware wallets to the humble paper wallet, from sophisticated multisig setups to regulated ETFs and fireproof crypto steel backups, there is no one-size-fits-all way to store crypto. Your ideal method depends on your technical comfort, threat model, and investment goals.
For sovereign holders who value decentralization, a combination of cold hardware storage, metal seed backups, and multisig can provide robust protection. For those prioritizing convenience and integration with traditional finance, ETFs and custodial solutions may be more appropriate—though they sacrifice direct ownership.
In cryptocurrency, security is a mindset. The best storage strategy is the one that balances your need for safety, access, and peace of mind, while acknowledging the irreversible nature of blockchain transactions.